Designing a Flexible Remote Support Access
Giving users the power to define secure, compliant region-specific remote access across international support teams.

Overview
The Remote Support Access initiative was part of my work within the Identity and Access Management (IAM) team at TOPdesk, a SaaS platform supporting organizations worldwide. The goal was to strengthen data protection and user trust by allowing customers to control which regional support branches could access their environments remotely. This project bridged the gap between operational efficiency for our support teams and compliance obligations for customers handling sensitive data under region-specific regulations like GDPR.
As TOPdesk expanded its international support operations, customers increasingly needed to ensure that their data was handled only within approved geographic regions. Some organizations, particularly in the public sector or regulated industries, required fine-grained control over which support teams could access their environments. The existing remote support model was globally functional but lacked flexibility and transparency for region-specific compliance needs.
The IAM team’s mission was to design a secure, scalable model that allowed customers to define and manage access by region, without creating additional friction for daily support operations,
Context
Problem
While our support agents had the necessary access to assist customers, the lack of location-based control raised compliance concerns for organizations operating under strict data protection laws.
Specifically:
Customers couldn’t limit access by geographic region or branch location.
Support teams needed a simple way to comply with customer-driven restrictions.
The system had to ensure security and consistency across multiple regions while remaining easy to configure.
In essence, we needed to balance compliance control for customers with operational consistency for TOPdesk’s global support structure.
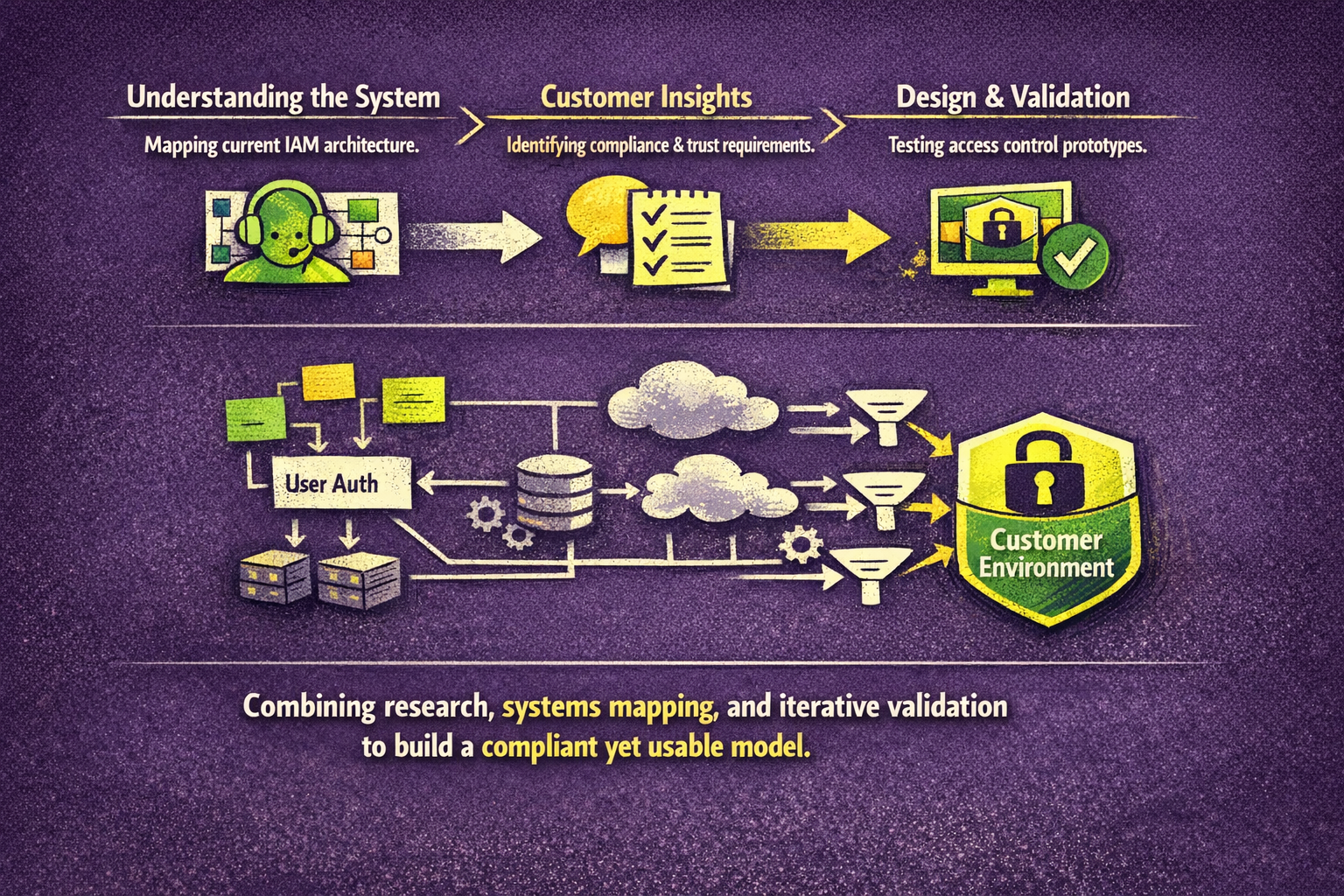
Process
1. Understanding Context and Constraints
I started by mapping the current remote support workflow and identifying where access control logic existed in the system architecture. This involved collaboration with IAM architects, security specialists, and support operations to understand both technical dependencies and compliance requirements.
2. Research and Discovery
We conducted exploratory sessions with customer success partners and enterprise clients representing different regions. From these conversations, we learned that:
Customers wanted autonomy over where their data was accessed.
Many preferred an “allow-list” approach, defining which support locations were authorized.
The UI needed to translate technical access models into understandable business controls.
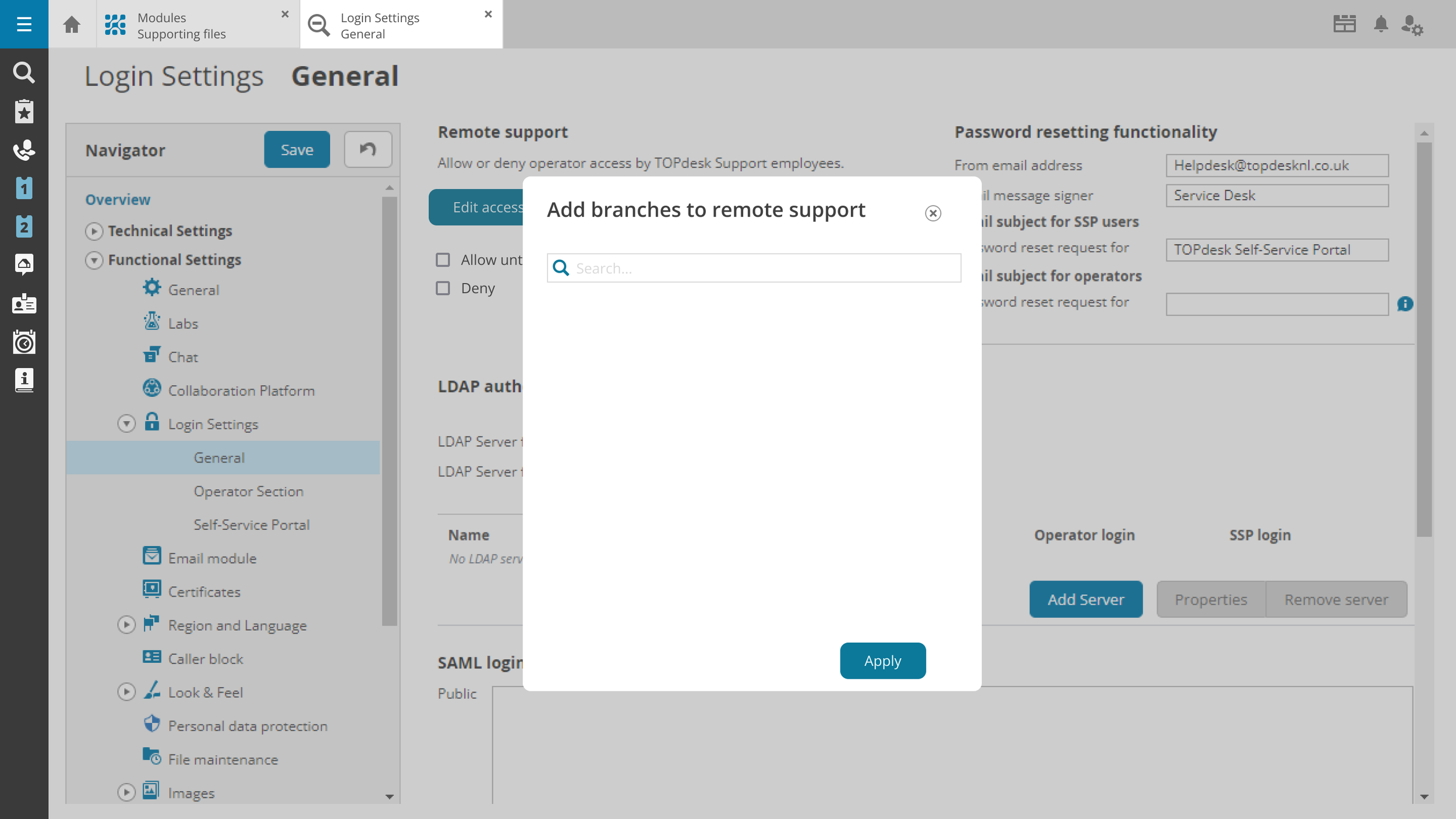
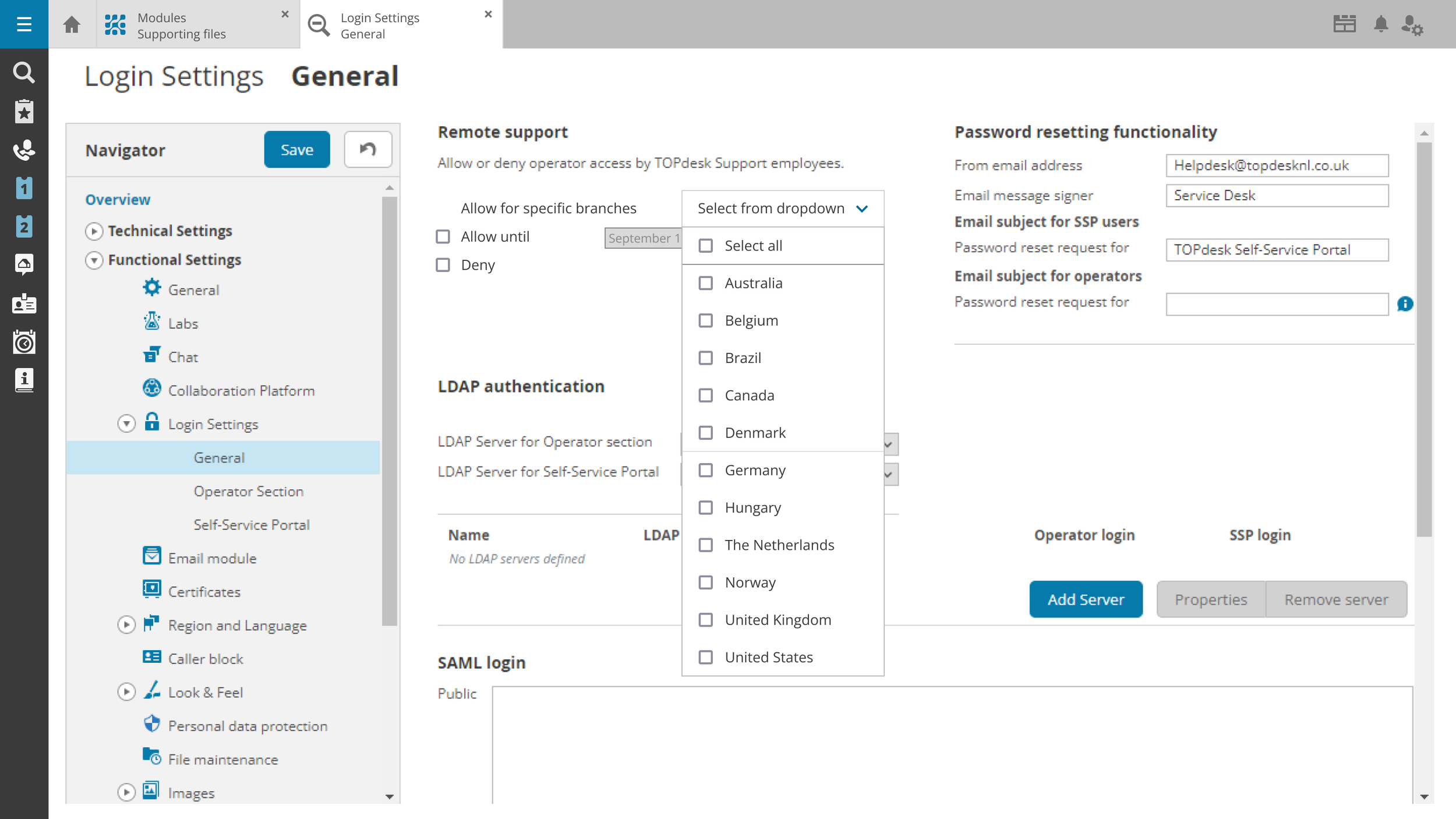
3. Concept and Design Development
Based on insights, I designed several conceptual models for how customers could set access preferences:
A geographic selector to specify approved support branches.
Transparent status indicators showing which regions currently had access.
Clear feedback for both customers and internal support teams when access was restricted.
Early prototypes explored varying levels of complexit, from simple toggles to rule-based access policies. Through design reviews and technical alignment, we refined the approach to a region-based selection model, balancing simplicity and control.
4. Alignment and Validation
I co-facilitated review sessions with stakeholders from security, compliance, and engineering to validate our assumptions. We iterated on interaction patterns to ensure consistent terminology and error feedback across all IAM modules. The final prototype was reviewed with international support team leads to confirm operational feasibility.
5. Preparing for Implementation
Collaborating with engineering, I helped structure handover documentation and behavior specifications to ensure correct handling of edge cases, such as users switching regions or emergency access scenarios.
Outcomes
The new Remote Support Access feature gave customers clear, auditable control over which support regions could access their environments. This not only improved compliance with regional data protection laws but also strengthened customer trust and transparency.
Key improvements:
Introduced per-region access selection aligned with customer location policies.
Enhanced clarity through explicit visibility of current access permissions.
Reduced compliance risk for enterprise customers and public sector clients.
Improved confidence between support teams and customers, reducing approval delays.
Internally, the design also provided a scalable foundation for future multi-region access management, setting a precedent for other IAM functionalities.